Filters
Stock royalty-free photos and images of Хакери
Discover unlimited high resolution images of Хакери and stock visuals for commercial use.

Picture of an hacker on a laptop

Hacker with his computer on dark background

Hacker on a computer

Masked anonymous hacker is pointing on Cyber attack.

Computer crime silhouette Hacker typing on computer in a dark room. Working on binary code technology. binary data, computer crime and network security concepts.

Binary code with SECURITY and magnifying lens on white background

Progress Bar Loading with the text: Spying

Close up view on gavel and computer keyboard. Internet security laws concept.

Shocked Woman Covering her Mouth with her hand. Binary code over the face. Image edges cut out.

Cyber Crime Concept Illustration. Professional Hackers in Black Masks Blended with Financial Related Images. Online Financial Safety Concept

Piece of paper with info on hook!

Computer hacking

Young hacker no face on black background.

Serious hipster computer programmer developing app while composing code and sitting at table with switched lamp, overworking concept

Corporate Female Executive smashing notebook

A 3d rendering to illustrate a malware or a virus in a binary code

Folders and files under the protection from hacking

Computer security concept : digital cyber hacker use laptop stealing ransomware data server ,selective focus

Internet crime concept. Dangerous hacker in hoodie shirt and dark digital background around stealing your data.

Smartphone with a padlock on it that says "privacy". Data security, which are contained in your electronic devices.

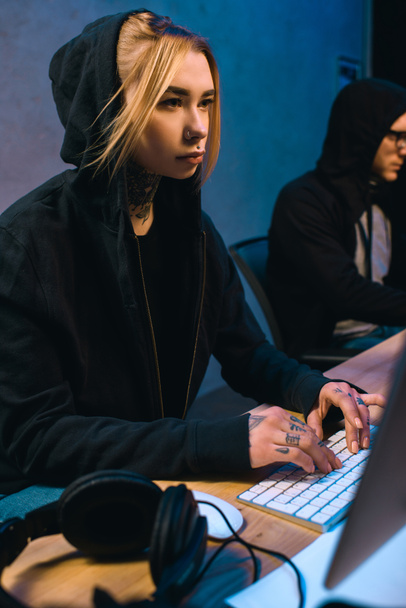
Medium shot of a hacker team working in a dim basement

Medium shot of a hacker using VR gloves and headset

Hacker with his mobile on isolated white background

Hacker in data security concept. Hacker using laptop. Hacking the Internet. Cyber attack.

Anonymous hacker in the hoodie, breaks the access to steal information and infect computers and systems. the concept of hacking and cyber war
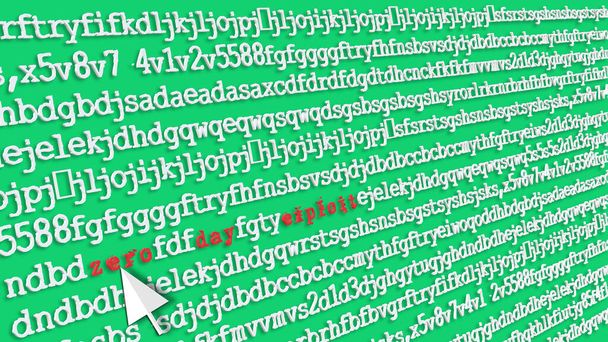
In the jargon of computer security, zero-day exploit. Computing vulnerability. 3D illustration of random letters and highlighting the poster design concept. Mouse arrow. Perspective and depth.
Masked anonymous hacker is pointing on DDoS Attack

Binary code with HACKED and magnifying lens on black background

Binary code with ENTER and magnifying lens on black background
Binary code with RUBY and magnifying lens on black background - programming concept
Binary code with TROJAN VIRUS and magnifying lens on black background

Smartphone placed on a white surface, with a padlock on it. Security and inviolability of electronic devices and protection of their data.

Computers and monitors for cyber crimes and cyber attacks on a desk in a hackers dim room with lamps

Young cybercriminals hacking documents on modern computer and making cyberattack on government in equipped hacker hideout

Medium shot of young men hacking in a dim basement

Medium shot of young male hackers working at their desks

Index that confirms the secret code in the keyboard of an ATM to withdraw cash

Cyber Crime Meaning Virus Vulnerable And Crack
Cyber Crime Representing Threat Vulnerable And Fingerprint

Hacker Phishing Representing Malicious Hackers And Cyber

Spyware Hacked Indicating Attack Vulnerable And Unauthorized

Secure purchase with credit card

Hack Online Indicating Web Site And Cyber

Cyber Attack Threat By North Korea Hackers 3d Illustration. Shows Hack By Korea And Virus Or Online Web Security Threat To Data Protection

Russian Hacking Election Attack Alert 3d Illustration Shows Spying And Data Breach Online. Digital Hacker Protection Against Moscow To Protect Democracy Against Malicious Spy

Russia Hacking American Elections Data 3d Illustration Shows Kremlin Spy Hackers On Internet Attack Usa Election Security Or Cybersecurity

Hacker Typing Hacked Data Alert 3d Illustration Shows Cybersecurity Type Keyboard Programming By Russians On Dnc Computer In Usa

Website Hacked Cyber Security Alert 3d Illustration Shows Online Site Data Risks. Election Hacking Attacks On The Usa In 2018 And 2020 From Russia
Computer Hacker silhouette typing on computer in a dark room. Working on blue binary code technology. binary data, computer programming and network security concepts.

3D rendering abstract code in the virtual space. The computer code is bent in the form of a tape